The gap between the vendor discovering a vulnerability and the patch getting to you will always be an issue – this is the zero-day threat. It escalates if the threat actors became aware of the vulnerability and exploits it before the vendor becomes aware. Now research by Mandiant shows that, …
When redacting does not work
We all see redacting n the TV shows and movies we watch – documents with big black lines through the secret information that must not be revealed – and I use similar techniques for screenshots I use here to conceal secret information. I am sure you do the same. I …
CISA security advisory for Drupal
Drupal is a CMS platform, similar to WordPress, so it is out there on the internet, vulnerable for exploitation. So if you use Drupal get it patched: Drupal Releases Security Advisory to Address Vulnerability in Drupal Core | CISA Do you know if your organisation’s website is hosted on Drupal …
As promised yesterday…
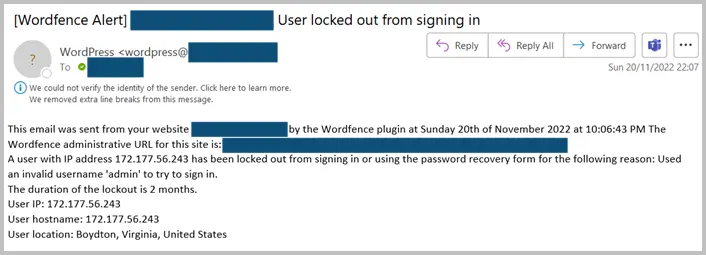
… more about extortion ransomware and what you can do about defending your information from it: From Encryption Ransomware To Extortion Ransomware Part I – CyberAwake This first part looks at defending critical accounts from compromise.
See what Elon Musk’s Twitter responses can do…
A couple of weeks back I posted a link to an article by Marianna Spring, the BBC’s Disinformation and social media correspondent, that examined how Twitter was functioning having now laid so many people off – many of whom appeared to be working as Twitter’s social conscience. Twitter, trolls, child …
Continue reading “See what Elon Musk’s Twitter responses can do…”