The issue of a trusted insider betraying a trust either maliciously or for commercial gain is a problem we often discussed at university and never really came up with an answer. You need trusted people for any business to operate – you should use the “principle of least privilege” to …
US Cybersecurity and Infrastructure Security Agency security advisories
The US Government’s CISA has released a range of security advisories, including updates required for VMware: VMware Releases Security Update | CISA CISA Updates Advisory on Threat Actors Exploiting Multiple CVEs Against Zimbra Collaboration Suite | CISA CISA has also been issuing advice for industrial systems. If you use these …
Continue reading “US Cybersecurity and Infrastructure Security Agency security advisories”
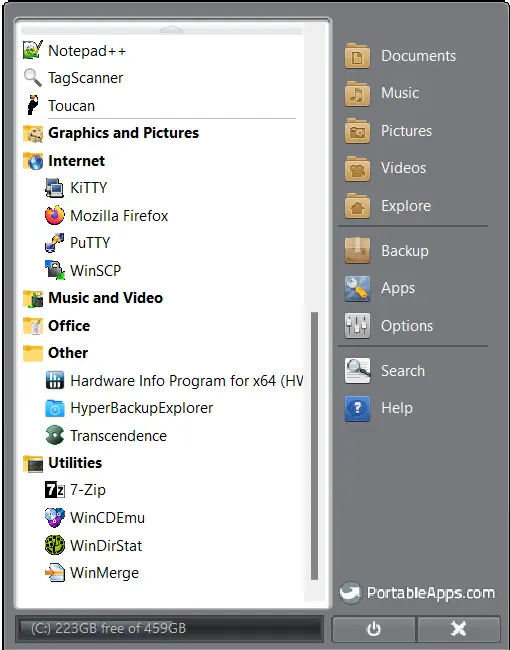
Why pirated software is not a good idea and PortableApps are.
Because it can be compromised and spread malware to you. Pirated 3DMark benchmark tool delivering info-stealer malware (bleepingcomputer.com) Just don’t do it. If you need a utility for free, try this site: PortableApps.com – Portable software for USB, portable, and cloud drives I do not guarantee the security of any …
Continue reading “Why pirated software is not a good idea and PortableApps are.”
Here is where automated law enforcement falls flat on its face
We have similar issues with the firewall security we maintain at a legal firm – some of the lawyers deal with distressing cases and our monitoring and filtering has to be done on a very granular level to enable their work but protect the rest of the users, and we …
Continue reading “Here is where automated law enforcement falls flat on its face”
Security concerns at Twitter
Twitter is a very popular promotional tool used by many businesses, now Peiter Zatko, a former security chief, has testified that Twitter has misled US regulators as to how secure the platform is: Twitter whistleblower alleges ‘egregious deficiencies’ in security measures | Twitter | The Guardian Bad news for us, …