Bug bounties are a useful way for vendors – and now government departments – to engage with honest, white hat, cyber security experts, to test systems for flaws. DoD issues call for hackers to dig into networks – The Record by Recorded Future
Near-undetectable malware
There are claims from Palo Alto Networks’ Unit 42 threat intelligence team that they have discovered a nearly undetectable strain of malware. The malware is contained in a CV for Roshan Bandara, but rather than the normal .pdf or Word file it is an image file -.iso. Near-undetectable malware linked …
Are you trying to improve your organisation’s cyber security? Lessons from the largest data theft ever. UPDATED 11 July 2022.
This post was first published on 5 July 2022. The Chinese President, Xi Jinping, is calling for improved cyber security, in the country following the unprecedented alleged data theft by ChinaDan: Security warning after sale of stolen Chinese data – BBC News Details of the theft are starting to be …
What is a cryptopocalypse?
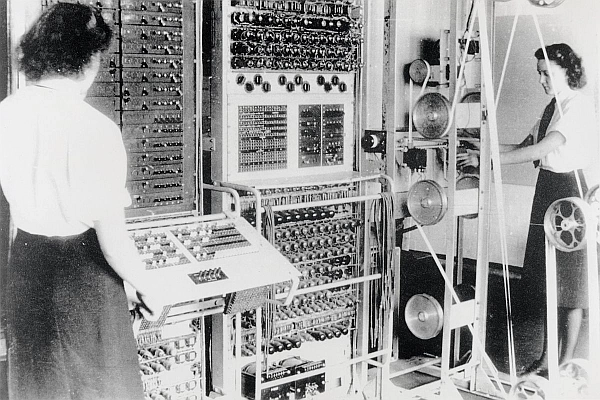
We have come a long way in cryptography and computing since the Colossus electronic computer, (above), was built at Bletchley Park, during the Second World War, to break the Lorenz cipher. With the advances in computing technology, there is a foreseeable point in the future, possibly only ten years, when …
National Cyber Security Centre Threat Report 8 July 2022
Back after a short break: Threat Report 8th July 2022 – NCSC.GOV.UK