CISA Adds Three Known Exploited Vulnerabilities to Catalog | CISA These alerts are for SAP NetWeaver.
Another example of using Bluetooth for something it was not intended for
Earlier this week, I wrote about the Bluetooth weaknesses that would allow someone to drive off with your Tesla: How to unlock a Tesla that does not belong to you! – Smart Thinking Solutions Here is a research paper, from UC San Diego, that examines how the cryptographic anonymity that …
Continue reading “Another example of using Bluetooth for something it was not intended for”
Stealth Linux malware – using new methods of evasion
The discovery of Linux backdoor malware is unusual as it uses stealth techniques that have not been seen before. This malware is extremely hard to detect as it does a very efficient job of cleaning the infected systems of any traces of it’s operations. Once infected the malware gives high …
Continue reading “Stealth Linux malware – using new methods of evasion”
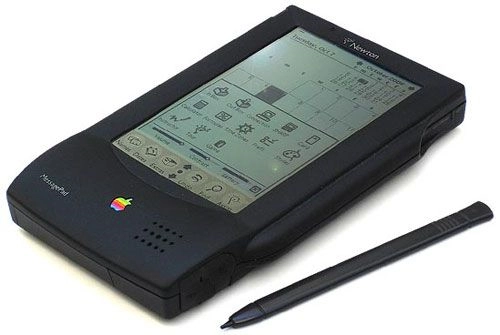
Because It’s Friday – Looking at Apple’s first PDA
I really wanted to include this in last week’s Platinum Jubilee Technology series, but neither Steve Jobs or Tim Cook were born in 1952 and I could not find any other 1952 link, so here it is as a “Because It’s Friday” blog: Remembering Apple’s Newton, 30 years on | …
Continue reading “Because It’s Friday – Looking at Apple’s first PDA”
Lack of knowledge will hamper anyone’s cyber security efforts
This equally applies to individuals, large and small organisations and government departments. The threat actors best friend, is when we all compartmentalise our cyber security issues, dealing with them quietly and behind closed doors – this includes trying to pay the cyber criminals off! This gives them the opportunity to …
Continue reading “Lack of knowledge will hamper anyone’s cyber security efforts”