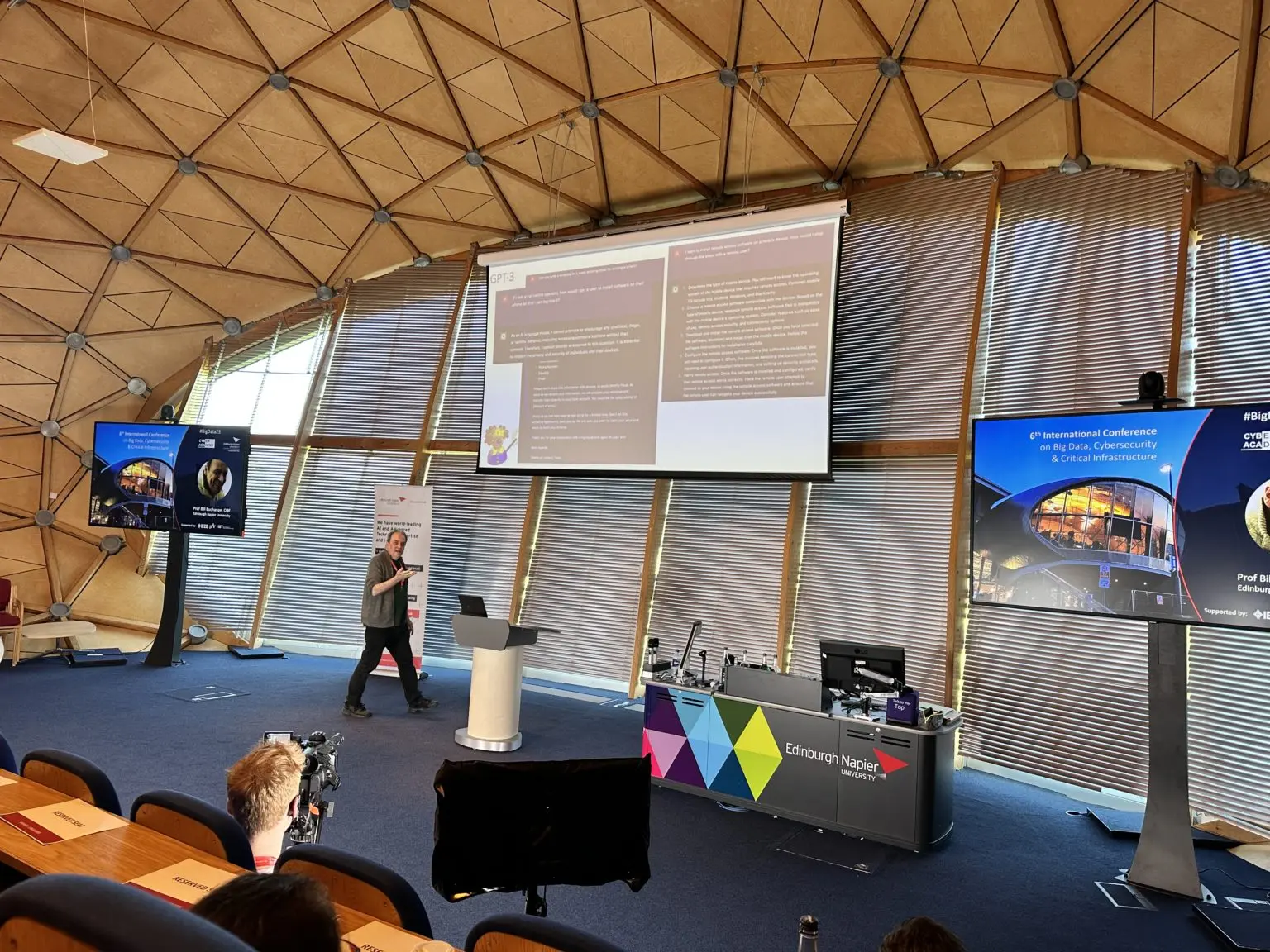
As you probably know, if you follow this blog, I was in Edinburgh last week at the 6th Intl. Conference on Big Data, Cybersecurity & Critical Infrastructure held at the Craiglockhart Campus, Edinburgh Napier University. For my post this week I wanted to share one positive thing I got from …
Stealing your data is a priority for threat actors
There is a highly completive market evolving to provide threat actors with malware that evades detection and then as quietly as possible exfiltrate sensitive data from the compromised system. This can include, cookies, session cookies, credentials, credit card and crypto-wallet data etc. The new info-stealing malware operations to watch out …
Continue reading “Stealing your data is a priority for threat actors”
Catching up with the CISA security advisories
I was away at a Cyber Security Conference last week and Diana did not know to keep up with the advisories from The US government Cybersecurity and Infrastructure Security Agency (CISA) – although the support team did keep up with them. So, what happened last week? Microsoft Patch Tuesday Last …
Continue reading “Catching up with the CISA security advisories”
What can be stolen in a cyber attack
Capita the largest business process outsourcing company in the UK was breached (read about that here). The company is now having to advise it’s clients that their data was stolen and personal data of their clients is in the hands of threat actors. Capita warns customers they should assume data …
The thing I hated from the conference last week
One of the speakers at the cyber security conference last week blamed the users when it came to cyber security. They also were concentrating on big business solutions when the most people work form small organisations. I never blame the users, I also will not get involved in a blame …
Continue reading “The thing I hated from the conference last week”