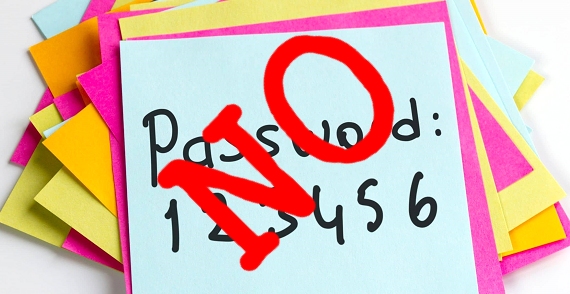
Is your password on this list? Before we start – the above statement sets the wrong tone for this article – it implies that you have a singular “password” but as we all know that is not true – you need many. However the social media people wanted that wording! …
National Cyber Security Centre Threat Report
Here is a link to the NCSC weekly threat report for week ending 19/11/2021: Weekly Threat Report – NCSC.GOV.UK
Do not click on the attachment – whatever it is called!
Before you open any attachment you should think about it: Are you expecting an attachment from this sender? Does this sender normally send you attachments like this? If you do not recognise the attachment extension then do not open it. Best practice is NOT TO OPEN any unexpected attachments! It …
Continue reading “Do not click on the attachment – whatever it is called!”
UK and US combined actions to strike back at ransomware
UK and US join forces to strike back in cyber-space – BBC News Among countering other cyber security threats to both the US and UK, ransomware attacks launched by shared adversaries will be high on the agenda.
ATM scams and some common sense cyber security defence tactics
The FBI has reported scams being run involving victims transferring money from their accounts having been provided with a QR code by the scammers to facilitate the transfer. To their crypto-currency wallets. https://www.ic3.gov/Media/Y2021/PSA211104 This was reported by Bruce Schneier. Wire Fraud Scam Upgraded with Bitcoin – Bruce Schneier Just make …
Continue reading “ATM scams and some common sense cyber security defence tactics”