… more about extortion ransomware and what you can do about defending your information from it: From Encryption Ransomware To Extortion Ransomware Part I – CyberAwake This first part looks at defending critical accounts from compromise.
See what Elon Musk’s Twitter responses can do…
A couple of weeks back I posted a link to an article by Marianna Spring, the BBC’s Disinformation and social media correspondent, that examined how Twitter was functioning having now laid so many people off – many of whom appeared to be working as Twitter’s social conscience. Twitter, trolls, child …
Continue reading “See what Elon Musk’s Twitter responses can do…”
Extortion only – no encryption
Ransomware is known for encrypting your data then demanding money for the key to recover your information (probably). Then ransomware moved on to not only encrypting but stealing your information and then extorting another ransom from you to not release or sell your information. Now there is ransomware that skips …
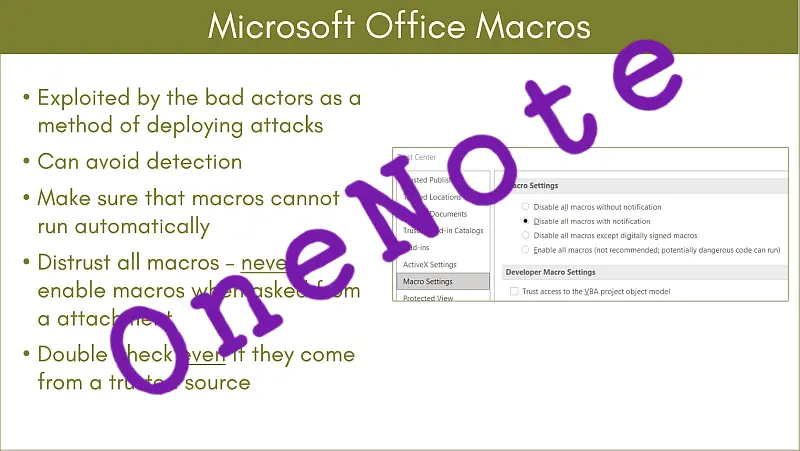
OneNote – the threat actors new best friend…
Once it had been discovered how straightforward it is to obscure a malicious package inside a OneNote .one attachment and mixed with “something new”, that users may not have seen before, it was obvious that the use of .one attachments for the delivery of malware was going to go up. …
Continue reading “OneNote – the threat actors new best friend…”
Another new UK agency for cyber security
We have the National Cyber Security Centre – why is this new agency not a department of that? UK creates new National Protective Security Agency • The Register It is a good idea to have a department with these specific responsibilities but a completely new agency – it is our …