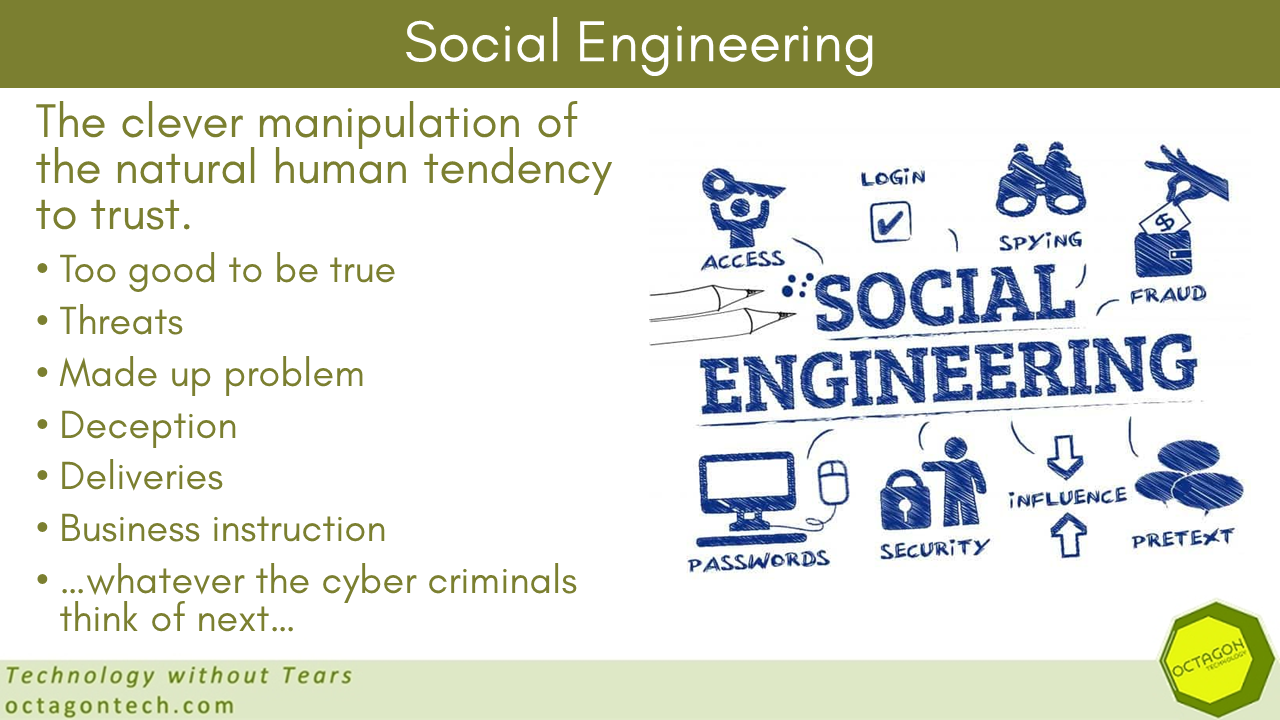
…just slow down. I often use the example of a successful social engineering/phishing email as one that arrives when you are under work pressure or just before before you want to leave for the weekend. Both are periods when the threat actors know your guard will be down – they …
WordPress vulnerabilities and you
Over the last two weeks we have had two WordPress jobs. One came about when our sysadmin discovered, during a routine system check, that a client’s site was using several insecure plugins. She contacted the client and their web designer and a disaster was averted – that web designer has …
More information on one of the LastPass security breaches
I have written before on the security breaches at the password vault LastPass: LastPass articles on Smart Thinking Solutions It has now been reported that one of only four people at the company who had access to the most sensitive data, was targeted via their home computer: LastPass says employee’s …
Continue reading “More information on one of the LastPass security breaches”
How do hackers get into secure networks?
Here is a clue – social engineering. I am often asked this by clients, especially those who I am suggesting need to up their cyber security game. Here is a very good article by the cyber security expert Brian Krebs looking in detail at the recent high profile data breaches …
Rishi Sunak and TikTok
TikTok is a Chinese company and concerns over the influence and access the Chinese government has to the information held by Chinese companies has led to official requests for the Prime Minister to ban the use of TikTok within government. Rishi Sunak faces calls to ban TikTok use by government …