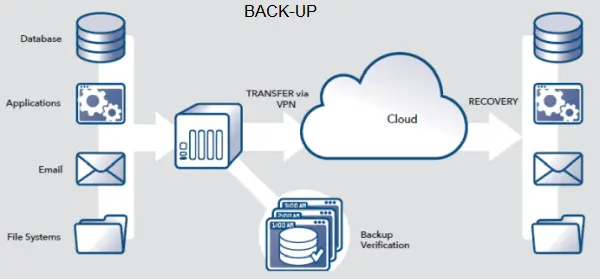
If you, that’s lucky as my latest article on CyberAwake explains just that:: WHAT EXACTLY DO I MEAN WHEN I SAY “RANSOMWARE RESILIENT BACK-UP”?
Because It’s Friday – two stories about code breaking
Well actually one story and one video. After five centuries these secrets are finally revealed Modern day computer technology got a kick start in World War II when it was developed to crack codes. Google Bletchley Park, where one of these crypto computers and Alan Turing were based, and watch …
Continue reading “Because It’s Friday – two stories about code breaking”
Fake Android app spotted by users but it still has a rating of 3.4 in the Google Play Store
Even though users are reporting that the app is fake in the reviews on Google Play Store, it is still available for download and getting positive ratings. Malicious Android app found powering account creation service (bleepingcomputer.com) The actions of the app to hijack account creation processes for major services such …
When does an app need access to your all your contacts?
Whenever I install an app and it asks for access to my contact list, it always sets off alarm bells for me. If I cannot see a valid reason for access, I will definitely deny the request and often will just delete the app. My contacts are mine and the …
Continue reading “When does an app need access to your all your contacts?”
Windows malware that can attack your phone
This attack by the pro-North Korean APT 37 espionage group has been aimed at specific targets. The malware exploits a backdoor in Windows and steals sensitive data from the infected PC and exfiltrates it to a Google Drive. ESET researchers also discovered the malware shows the capability to steal data …
Continue reading “Windows malware that can attack your phone”