Steganography When we were looking at steganography cyber attacks – hiding malicious code inside for instance image files – I was surprised just how much malware could be hidden without degrading the image. Here is a real-world example of this rare type if attack, spy are code embedded in a …
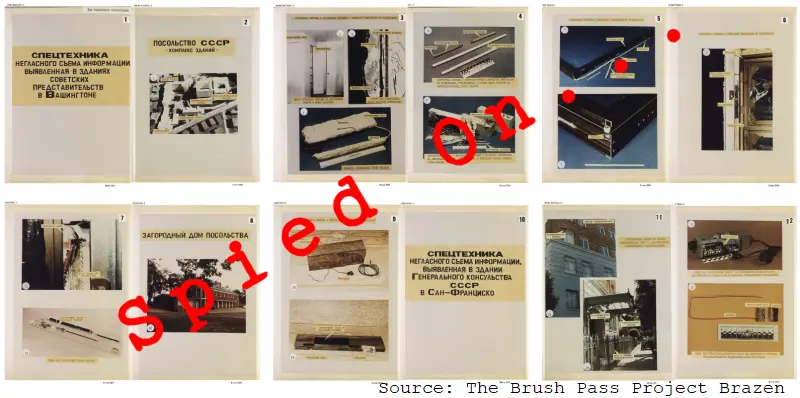
Cold War spying is a long way from today’s cyber-espionage weapons but they both successfully stole information.
This article comes via Bruce Schneier, and fits nicely into the Weekend Project – it is about security and has some connections to the posts we run here at Smart Thinking. Both Clive and I have attended Bruce Schneier speaking events, and through Clive’s links with Edinburgh Napier University have …
What is hell? – #BeCyberSmart
Weekends here at Smart Thinking is when we run background and more in depth, longer reads about cyber security and technology. So, we are starting our Cyber Security Awareness month – an event which will be all over social media – with an article about social media. As Clive often …
Do you operate an Exchange Server? Is it patched and up to date?
There is an actively exploited zero-day flaw being reported, that Microsoft has not yet patched – so have a look at GTSC’s blog post: Warning: New attack campaign utilized a new 0-day RCE vulnerability on Microsoft Exchange Server | GTSC (gteltsc.vn) The post also includes some temporary mitigation whilst waiting …
Continue reading “Do you operate an Exchange Server? Is it patched and up to date?”
Here is some of the open-source software I use – and it has all been targeted!
PuTTY, KiTTY and Sumatra PDF Reader – I did my due diligence before installing these – and now they have been targeted by ZINC, a state-sponsored group operating out of North Korea. ZINC weaponizing open-source software – Microsoft Security Blog Before writing this blog post I had checked my system …
Continue reading “Here is some of the open-source software I use – and it has all been targeted!”