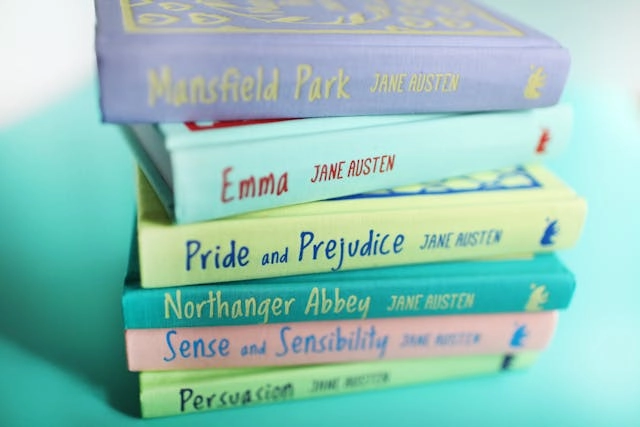
Fight Club is one of our son’s favourite movies so there was no way this article from The Conversation, by a number of academics, was not going to make the “Because it’s Friday” slot. Jane Austen fight club: experts go head-to-head arguing for her best leading man – The Conversation It is …
Jaguar Land Rover Cyber-attack
There are reports of the Jaguar Land Rover Group is suffering major outage because of a cyber security attack. Jaguar Land Rover production severely hit by cyber attack – BBC News The company has already issued a statement saying “there is no evidence any customer data had been stolen”. Of …
Back to Basics – Why MFA? (pt.3)
In this third part of my MFA mini-series, I am going to look at some of the resistance that we get when trying to implement multi-factor authentication. MFA – It is like medicine that tastes bad In the first part of this series, I briefly explained the highlights of why …
Something for the holidays
The holiday season is drawing to a close, but this scam that Bruce Schneier writes about will work at any time of the year. Baggage Tag Scam – Schneier on Security Your Takeaway This type of cyber-attack involving something that you should keep private, but you let get into the …
Sextortion
To get back in the swing of things after the summer break, let’s look at a particularly nasty cyber-attack – sextortion. To do this I am going to direct you to a series of articles on SANS Internet Storm by Jan Kopriva, looking at the attacks and how the money …