Let me clarify that statement. I really like the Apple App Store as a step in a cyber security plan. When your people have your organisation’s infomration on their devices – it is reassuring that those who are using Apple devices are getting their apps from a sorce that is …
It all starts with a phishing email
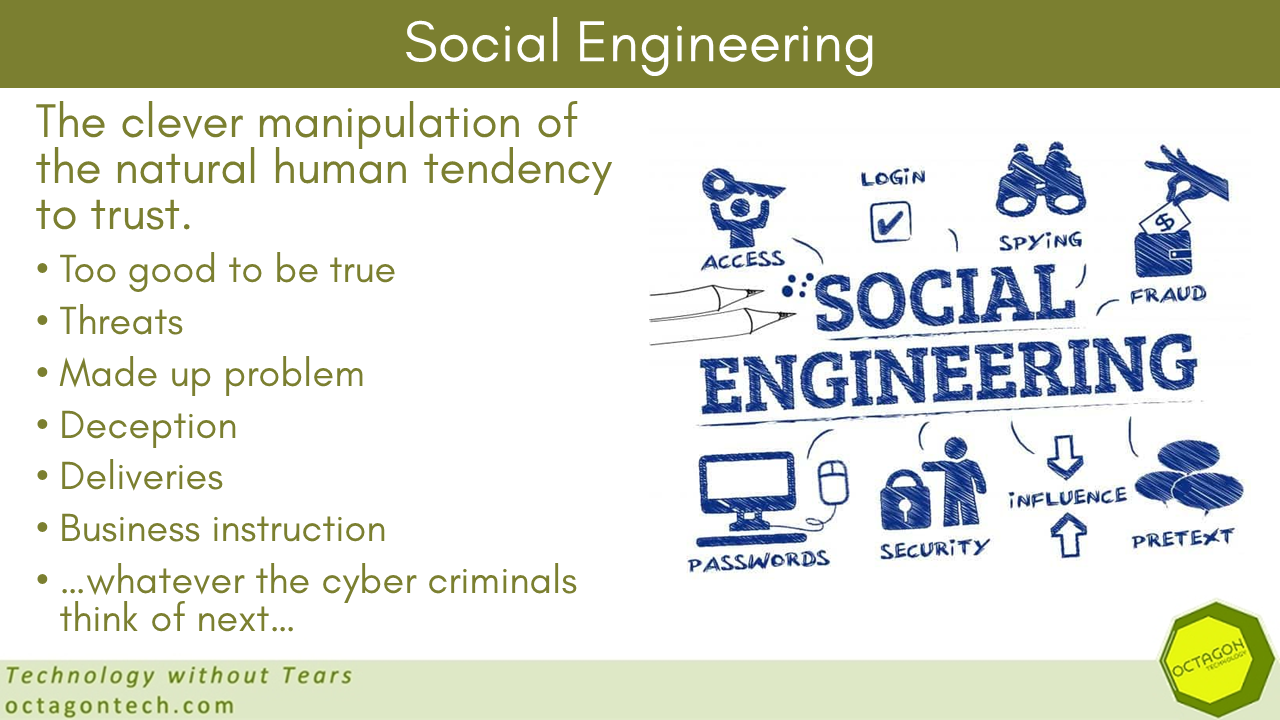
In most of our business cyber security training and work, we eventually get to the question of how cyber security defences are breached – and most often the answer is, using email. Even the biggest cyber criminal gangs attacking the highest profile targets, just use email. North Korean hackers attack …
More warnings about the possible spread of the Russian Ukraine cyber-conflict and NATO members are targets.
The European Union (EU) has issued a warning about the measurably increase in the volume of Russian cyber-attacks associated with the Russia Ukraine conflict and how these attacks can easily spread to other regions. Nations that actively support Ukraine, with whatever resources, are likely to be “at risk” of this …
Big Tech and EU lobbying
Here is a weekend read for you – grab a beverage of your choice and see what “big tech sums of money” can buy you: I saw first-hand how the tech giants seduced the EU – and undermined democracy | Georg Riekeles | The Guardian