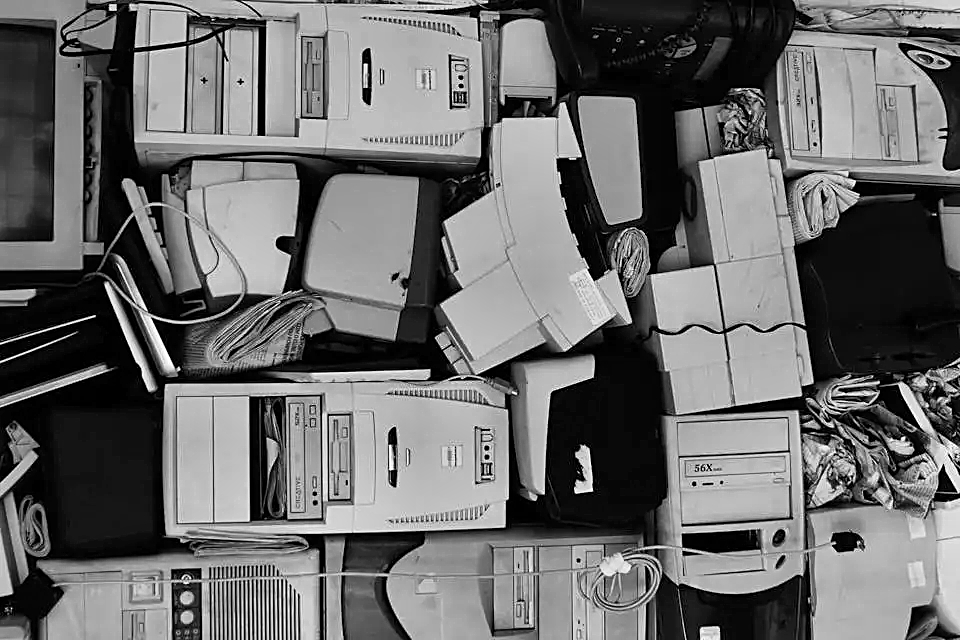
This is part 3 of a short series looking at information security in the office – here are links to part 1 and 2. Information Security in the Office (pt.1) The Printer is the Issue Information Security in the Office (pt.2) Forgotten Technology Today we are going to look at …
Continue reading “Information Security in the Office (pt.3)”