Over the past couple of weeks, I have been writing a short series looking at the basics of encryption, how you can use it to improve your cyber security and some of the issues you need to address if you are using it. As I have done with other mini-series …
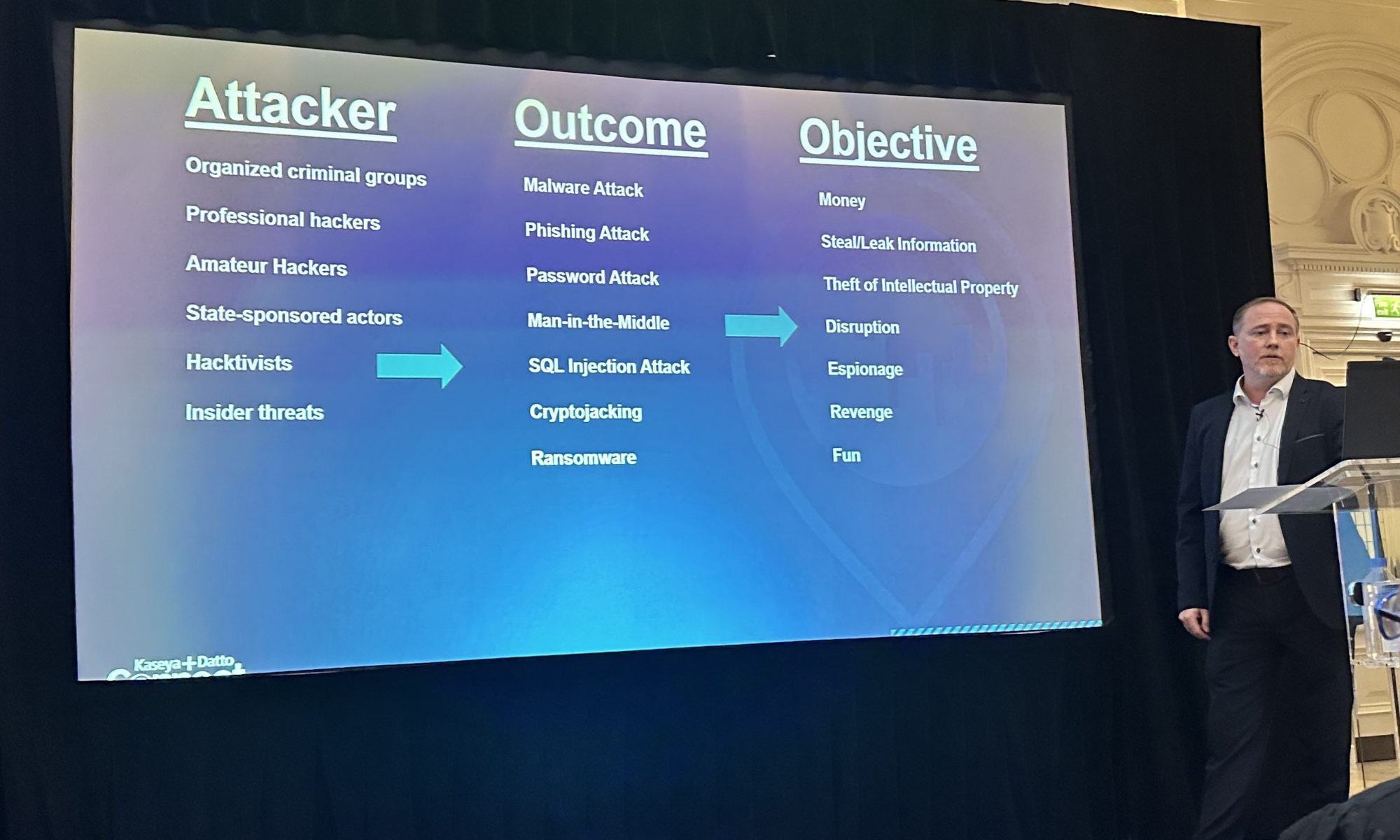
The fast track for better cyber security
Modern cyber security tools are well within the budget of even the smallest organisations- even one person businesses. We have a webinar this week to tell you how. This article will give you some background it includes a link to sign up for either the webinar or to get the …
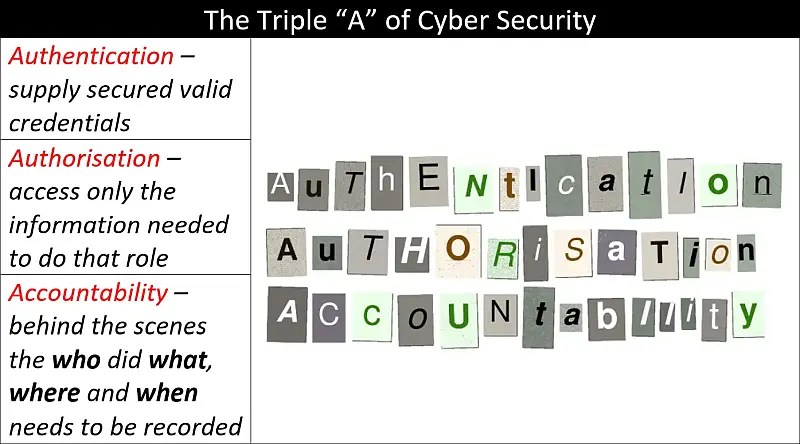
The Principle of Least Privilege and Authentication, Authorisation and Accountability – A Primer
Authentication, Authorisation and Accountability (AAA) and The Principle of Least Privilege (PoLP) come together in this primer to give you a basic understanding of the importance of knowing who is accessing your information and how much they can access. Another important idea covered here is what happens when something goes …
Keep It Simple… Encryption (pt. 4)
You use encryption to keep your information secret from unauthorised people – not from everyone. I am going to skip the basics of encryption here as I have covered it in parts 1-3, there are links to those articles at the end of this article. Today, having spent time telling …
Catching up with CISA
The US government Cybersecurity and Infrastructure Security Agency (CISA) is one of our go-to information sources for cyber security information. Here is a round-up of their latest alerts: Apple Released Security Updates for Safari and macOS | CISA Cisco Releases Security Updates for Multiple Products | CISA Fortinet Releases Security …
Keep It Simple… Encryption (pt. 1)
Today we are going to look at one of the quickest ways any organisation (that uses Microsoft 365) can enhance its cyber security – encryption. Why encryption? I was leading a Cyber Security Awareness course last week and one of the first things we discussed was best practice when it …
Manage and Patch that Hardware
It is so easy to forget about those boxes in the cupboard, that your organisation depends on. I often find routers, switches and other devices left off my initial investigation document when I start an IT and Cyber Security Audit. Here is the reason why you must make sure they …