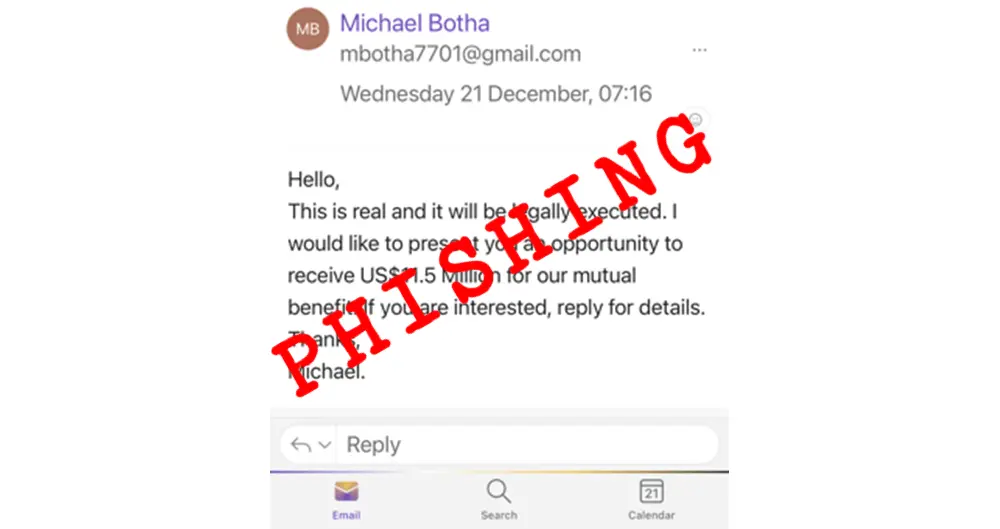
…but sometimes you do get fooled. Today I have published my first cyber security article, of 2023, over on our online training site CyberAwake. It is about a spam email that got through our email defences. Sometimes a simple email may work for the bad guys – CyberAwake Here is …
Phishing Infographic
The US government Cybersecurity and Infrastructure Security Agency (CISA) recently released an useful infographic highlighting many aspects of phishing cyber attacks: Phishing Infographic (cisa.gov) It also includes some good advice on how to deal with the threat.
Top cyber security threats for next year
I have been hanging onto this article for a few weeks now – and in a normal week this would be part of the weekend read project, but it is Christmas week and so you get the weekend on Thursday – you also got “Because It’s Friday” on Thursday! All …
Some Seasonal Training over on CyberAwake
Just in time for Christmas – I have an article, published yesterday, over on our inline training site, CyberAwake, with a few tips on tightening your cyber security before heading off for your Christmas break. Christmas cyber security advice – CyberAwake In particular I offer some advice on controlling that …
Continue reading “Some Seasonal Training over on CyberAwake”
Google action to protect small businesses
Google is recognising the impact its services have on the success of smaller businesses, and how scammers are taking advantage to exploit those same businesses. The article covers the legal actions Google has taken; the scams that are being run in its name and advice on how to deal with …
Continue reading “Google action to protect small businesses”