Guernsey’s Data Protection Commissioner Brent Homan has published a report showing that the leaking of personal data on the island has risen. More than 1,000 people affected by data breaches – BBC The Office of the Data Protection Authority (ODPA) says over 1500 people have been impacted. The reported stated …
Back to Basics – The Collection II
This week the Wednesday Bit is for reminding you about my collection of mini-series and back to basics cyber security primers. There have been a number of additions, updates and changes since I first ran a “Collection” article. Why am I doing this? Because we can all benefit from some …
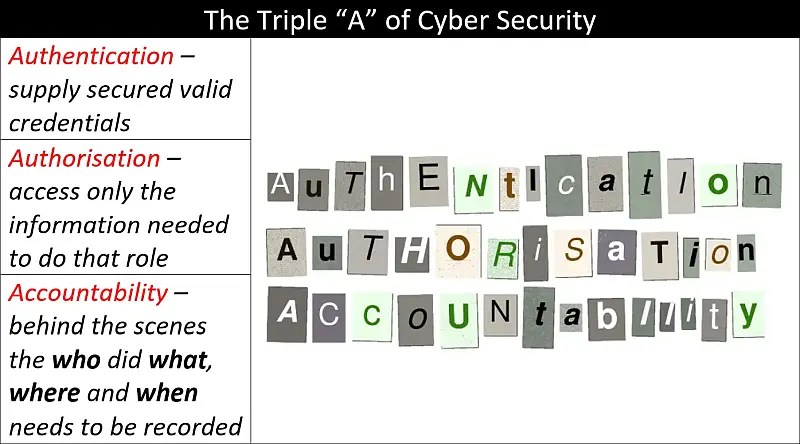
The Principle of Least Privilege and Authentication, Authorisation and Accountability – A Primer
Authentication, Authorisation and Accountability (AAA) and The Principle of Least Privilege (PoLP) come together in this primer to give you a basic understanding of the importance of knowing who is accessing your information and how much they can access. Another important idea covered here is what happens when something goes …
Keep It Simple… Encryption (pt. 1)
Today we are going to look at one of the quickest ways any organisation (that uses Microsoft 365) can enhance its cyber security – encryption. Why encryption? I was leading a Cyber Security Awareness course last week and one of the first things we discussed was best practice when it …
What the “Principle of Least Privilege” does for you? (pt. 1)
This article follows on from last week’s Why the “Principle of Least Privilege” works and something for free…. If you want the something for free, then you had better read that article first! Let’s start with a simple definition. The Principle of Least Privilege (PoLP) is a fundamental concept in …
Continue reading “What the “Principle of Least Privilege” does for you? (pt. 1)”