Once it required a level of technical skill, practice and hardware resources to carry out successful cyber attack that would make (illicit) money. Now researchers have discovered and easy to use framework that enables any would be hacker to craft sophisticated attacks, deploy them, steal information and monetise them: New …
Threat actors promise you something that is too good to be true…
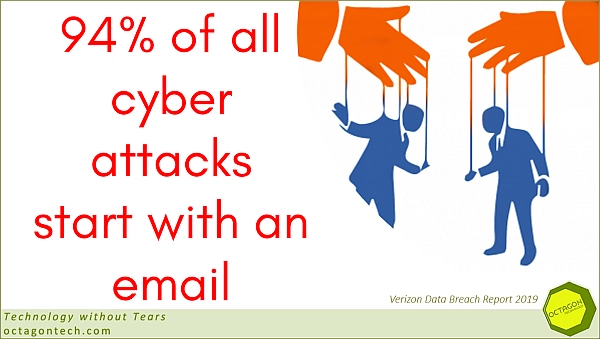
One of the key points we cover in our online and real-world cyber security awareness training is that threat actors will exploit human trust and fears. So phishing messages will contain: a threat – your tax bill is overdue see the fine here something nice – we over charged your …
Continue reading “Threat actors promise you something that is too good to be true…”
Ransomware highlights from Bleeping Computers
There are a rush of ransomware stories on Bleeping computers, mainly high profile organisations being hit, not only with crypto-malware but being blackmailed over data exfiltrated by the threat actors. Automotive supplier breached by 3 ransomware gangs in 2 weeks (bleepingcomputer.com) Hacker uses new RAT malware in Cuba Ransomware attacks …
Continue reading “Ransomware highlights from Bleeping Computers”
Phishing email alert – Excel spreadsheets loaded with RATs
Fortinet’s FortiGuard Labs threat intelligence have been tracking phishing emails that contain a triple threat of remote access trojans – RATS. The package is contained in an infected Microsoft Excel document and once the recipient of the email makes the mistake of opening the file – because the file name …
Continue reading “Phishing email alert – Excel spreadsheets loaded with RATs”
Budget friendly malware increases your risk
When breaking into a computer system cost significant money and resources, only a few capable individuals and groups did it. Now with the availability of cloud services and mass distribution the best resourced cyber gangs are turning to a gig economy model, combined with the IT “as-a-service” model to sell …
Continue reading “Budget friendly malware increases your risk”