…just slow down. I often use the example of a successful social engineering/phishing email as one that arrives when you are under work pressure or just before before you want to leave for the weekend. Both are periods when the threat actors know your guard will be down – they …
How do hackers get into secure networks?
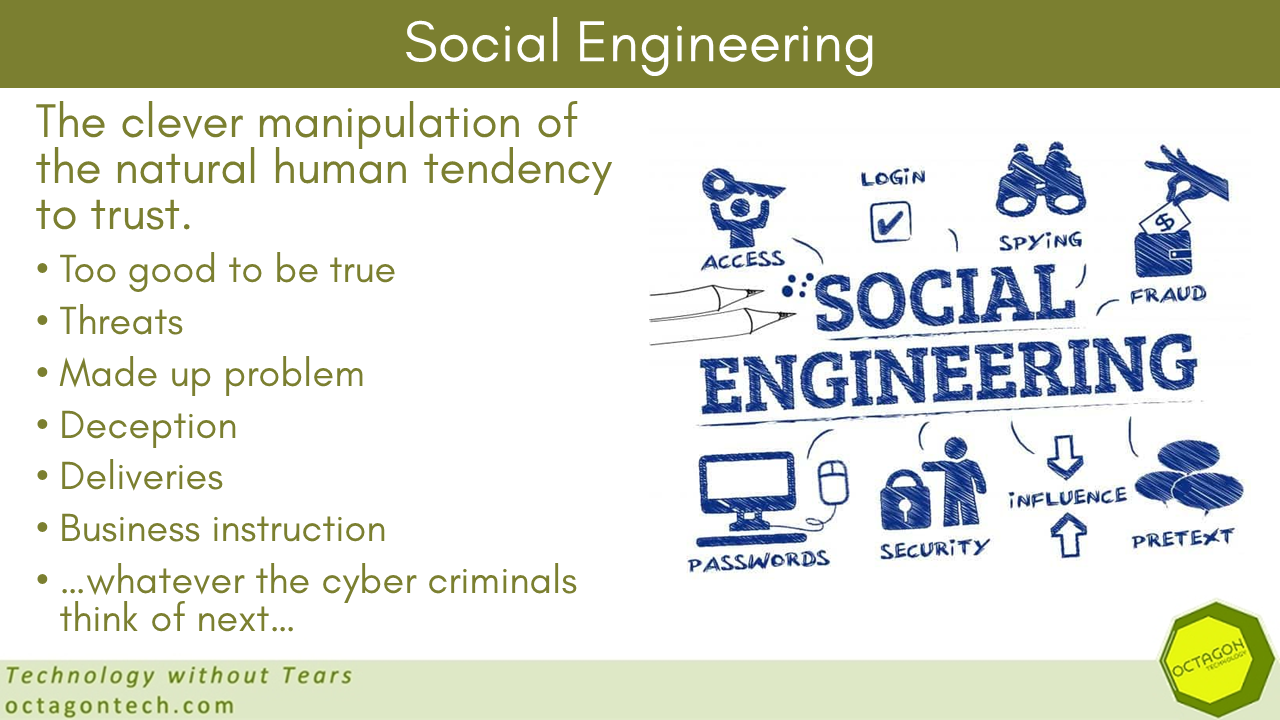
Here is a clue – social engineering. I am often asked this by clients, especially those who I am suggesting need to up their cyber security game. Here is a very good article by the cyber security expert Brian Krebs looking in detail at the recent high profile data breaches …
Would you be taken in?
I have written a lot about the fact that many cyber attacks include an element of social engineering, to tease the victim into lowering their guard and doing what the threat actor wants. Here is an excellent example of that, described by Xavier Mertens on SANS Internet Storm, where the …
Part 4 of my Ransomware mini-series was published yesterday
Yesterday I published part 4 of this ongoing series about ransomware on our online training site CyberAwake: Detecting Ransomware – Ransomware Part 4 – CyberAwake Part 5 has been published today, here: Ransomware – What Not To Do! – Smart Thinking Solutions The articles are about 600 words in length …
Continue reading “Part 4 of my Ransomware mini-series was published yesterday”
Royal Mail ransomware attack – no data exposed yet…
Following the ransomware attack earlier this year, the deadline for Royal Mail to pay the LockBit ransomware gang has passed and the Gang has not released any of the stolen data… yet. Experts think this s because they have not yet given up the hope of monetising the attack: LockBit’s …
Continue reading “Royal Mail ransomware attack – no data exposed yet…”