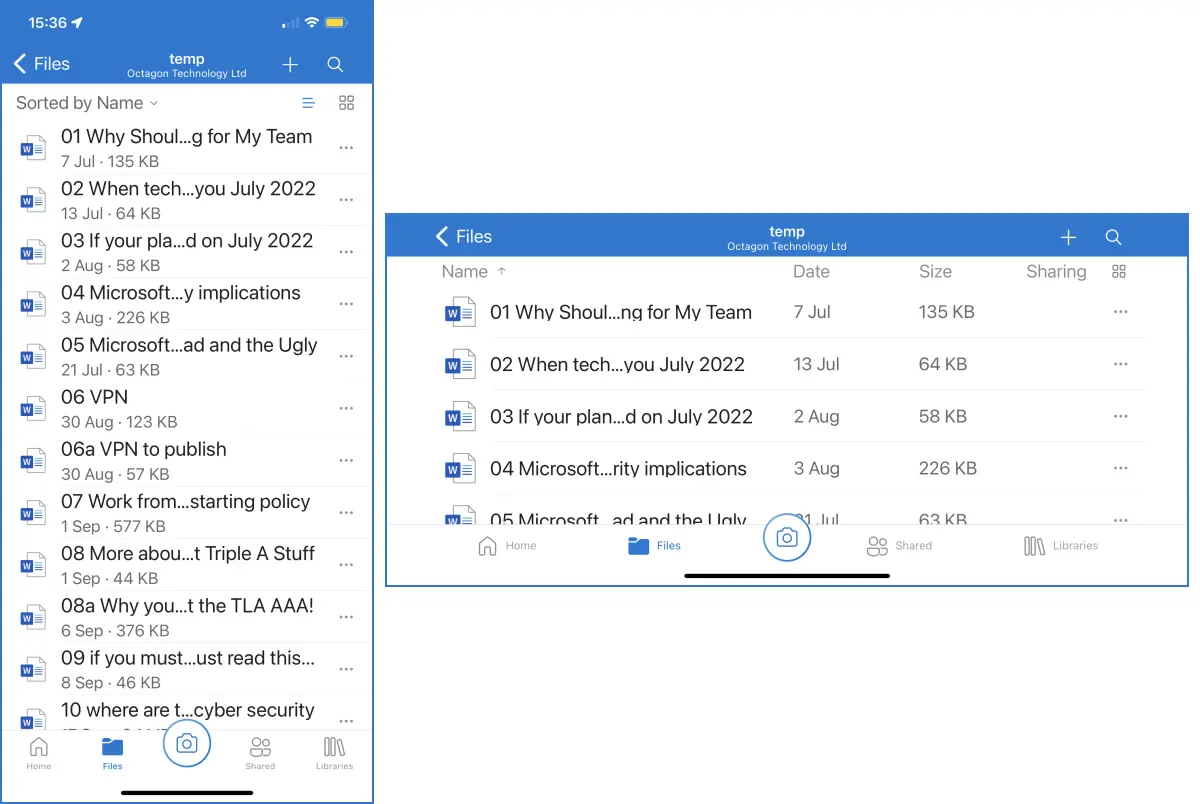
What does that rambling title actually mean? I use OneDrive and SharePoint for storing nearly everything, and I give files long file names. Who remembers to days when we had to name that file in eight characters? So, when I am browsing for a in portraits mode, the first part …
More privacy issues for Twitter
Following the revelations by Peiter Zatko, the former head of security at Twitter: Is Twitter a decade behind in its security practices? – Smart Thinking Solutions It now emerges that one of the essential steps in a Twitter password reset – logging out of any and all devices already logged …
Another case of a false positive and why we must not let these incidents weaken our cybersecurity stance
The highly respected security software vendor Malwarebytes, slipped up this time, classifying Google and YouTube as malware for short time: Malwarebytes mistakenly blocks Google, YouTube for malware (bleepingcomputer.com) I recently wrote about false positives and their possible impact on the cyber security stance of an organisation – if you did …
The ups and downs of ransomware software development
Threat actors are always changing their malware and tactics to evade the technical solutions the anti-virus and other security solution vendors distribute. So it is no surprise that malware gets patches and updates as well: Colonial Pipeline hackers add startling new capabilities to ransomware operation – The Record by Recorded …
Continue reading “The ups and downs of ransomware software development”
Credential stuffing attacks
This research by Okta highlights the issue of users recycling passwords: Okta: Credential stuffing accounts for 34% of all login attempts (bleepingcomputer.com) There were more login attempts by threat actors than legitimate ones! They were just trying out passwords to see if someone was stupid, (sorry if you do not …